Max Newman

Max Neumann (Newman), the only child of Herman Alexander Neumann, a German working in London, and his wife, Sarah Ann Pike, an elementary schoolteacher, on 7th February 1897. He went to the City of London School, and in 1915 he gained a scholarship to St John's College, Cambridge.
During the First World War he changed his name to Newman by deed poll. He joined the British Army and at the end of the war he returned to his studies. Jack Good has explained: "In 1921 he was a wrangler in part two of the mathematical tripos, with a distinction in Schedule B. He was elected to a fellowship at St John's in 1923 and appointed a university lecturer in 1927. Newman was among the pioneers of combinatory (or geometric) topology and wrote important papers on it in the late 1920s." (1)
Gordon Welchman attended lectures by Newman: "As an undergraduate at Cambridge University in 1925-28, I had been inspired by Newman's lectures on topology." (2) Alan Hodges has pointed out that by the late 1920s Newman was the foremost British exponent of topology. "This branch of mathematics could be described as the result of abstracting from geometry such concepts as 'connected', 'edge' and 'neighbouring' which did not depend upon measurement. In the 1930s it was unifying and generalising much of pure mathematics." Hodges claims that Newman was seen as a "progressive figure" in Cambridge University. (3)
Max Newman & Alan Turing
In 1934 Alan Turing attended a lecture given by Max Newman where he explained the work of German mathematician, David Hilbert. As Newman later pointed out: "The Hilbert decision-programme of the 1920's and 30's had for its objective the discovery of a general process, applicable to any mathematical theorem expressed in fully symbolitical form, for deciding the truth or falsehood of the theorem... Many were convinced that no such process was possible, but Turing set out to demonstrate the impossibility rigorously." (4)
Turing published his paper in April 1936. As Nigel Cawthorne pointed out: "What he produced was remarkable... When Newman, in his lecture, described Hilbert's 'definite method' as a 'mechanical process', he started an idea in Turing's head the future repercussions of which would be immense. The word 'mechanical' it its original sense, had referred to manual occupation, to work performed by human beings. By the 1930s, however, mechanical meant gears, rotors, vacuum tubes. It meant a machine. Turing took both definitions to heart." (5)
Bletchley Park
During the Second World War Newman joined the Government Code and Cypher School at Bletchley Park. In September 1942 he was placed in charge of a research section that was known as the "Newmanry". (6) He was given the problem of dealing with the Lorenz SZ40 machine that was used to encrypt communications between Adolf Hitler and his generals. It operated in a similar way to the Enigma Machine, but the Lorenz was far more complicated, and it provided the Bletchley codebreakers with an even greater challenge. In 1943 Newman came up with a way to mechanise the cryptanalysis of the Lorenz cipher and therefore to speed up the search for wheel settings. (7)
Alan Turing suggested that Newman worked with Tommy Flowers, a young telephone engineer, who had helped in building a decoder in 1941. (8) Flowers explained the objective of Newman's machine: "The purpose was to find out what the positions of the code wheels were at the beginning of the message and it did that by trying all the possible combinations and there were billions of them. It tried all the combinations, which processing at 5,000 characters a second could be done in about half an hour. So then having found the starting positions of the cipher wheels you could decode the message." (9)
Colossus Mark I
The initial machine designed by Newman kept on breaking down. Flowers later recalled: "I was brought in to to make it work, but I very soon came to the conclusion that it would never work. It was dependent on paper tape being driven at very high speed by means of spiked wheels and the paper wouldn't stand up to it." Flowers suggested that Newman used valves instead of the old-fashioned electromechanical relay switches that had been used in Turing's machines. He claimed valves would do the same job much faster without the need for the synchronisation of the two tapes.
Gordon Welchman, a colleague at Bletchley Park, pointed out: "Flowers seems to have realized at once that synchronization 44 punched-tape operations need not depend on the mechanical process of using sprocket holes. He used photoelectric sensing, and at that early date he had enough confidence in the reliability of switching networks based on electronic valves (tubes, in America), rather than electromagnetic relays, to risk using such techniques on a grand scale. From his prewar experience, Flowers knew that most valve failures occurred when, or shortly after, power was switched on, and he designed his equipment with this in mind. He proposed a machine using 1,500 valves." (10)
Tommy Flowers claimed that Newman and his team of codebreakers were highly sceptical of his suggestion: "They wouldn't believe it. They were quite convinced that valves were very unreliable. This was based on their experience of radio equipment which was carted around, dumped around, switched on and off, and generally mishandled. But I'd introduced valves into telephone equipment in large numbers before the war and I knew that if you never moved them and never switched them off they would go on forever. They asked me how long it would take to produce the first machine. I said at least a year and they said that was terrible. They thought in a year the war could be over and Hitler could have won it so they didn't take up my idea." (11)

The project was now shelved. However, Flowers was so convinced that he could get Newman machine to work effectively he continued building the machine. At the Post Office's research centre at Dollis Hill, North London, Flowers took Newman's blueprint and spent ten months turning it into the Colossus Computer, which he delivered to Bletchley Park on 8th December 1943, but was not fully operational until 5th February 1944. It consisted of 1,500 electronic valves, which were considerably faster than the relay switches used in Turing's machine. However, as Simon Singh, the author of The Code Book: The Secret History of Codes & Code-Breaking (2000) has pointed out than "more important than Colossus's speed was the fact that it was programmable. It was this fact that made Colossus the precursor to the modern digital computer." (12)
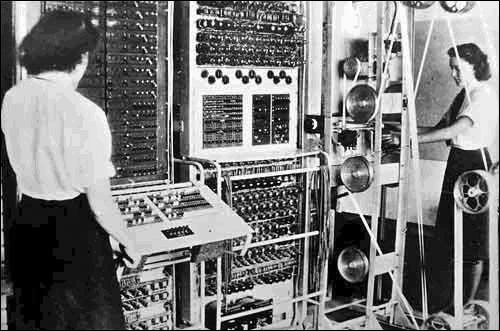
Newman's staff that operated the Colossus consisted of about twenty cryptanalysts, about six engineers, and 273 Women's Royal Naval Service (WRNS). Jack Good was one of the cryptanalysts working under Newman: "The machine was programmed largely by plugboards. It read the tape at 5,000 characters per second... The first Colossus had 1,500 valves, which was probably far more than for any electronic machine previously used for any purpose. This was one reason why many people did not expect Colossus to work. But it began producing results also immediately. Most of the failures of valves were caused by switching the machine on and off." (13)
Harry Fensom later reported: "The Colossi were of course very large, hence their name, and gave off a lot of heat, ducts above them taking some of this away. However, we appreciated this on the cold winter nights, especially about two or three in the morning. When I came in out of the rain, I used to hang my raincoat on the chair in front of the hundreds of valves forming the rotor wheels and it soon dried off. Of course it was essential that the machines were never switched off, both to avoid damaging the valves and to ensure no loss of code-breaking time. So there was an emergency mains supply in the adjoining bay which took over automatically on mains failure." (14)
Colossus Mark II
In February, 1944, the Lorenz SZ40 machine was further modified in an attempt to prevent the British from decyphering it. With the invasion of Europe known to be imminent, it was a crucial period for the codebreakers, as it was vitally important for Berlin to break the code being used between Adolf Hitler in Berlin and Field Marshal Gerd von Rundstedt, the Commander-in-Chief of the German Army in western Europe. (15)
Max Newman and Tommy Flowers now began working on a more advanced computer, Colossus Mark II. Flowers later recalled: "We were told if we couldn't make the machine work by June 1st it would be too late to be of use. So we assumed that that was going to be D-Day, which was supposed to be a secret." The first of these machines went into service at Bletchley Park on 1st June 1944. It had 2,400 valves and could process the tapes five times as fast. "The effective speed of sensing and processing the five-bit characters on punched paper tape was now twenty-five thousand characters per second... Flowers had introduced one of the fundamental principles of the postwar digital computer - use of a clock pulse to synchronize all the operations of his complex machine." (16) It has been pointed out that the speed of the Mark II was "comparable to the first Intel microprocessor chip introduced thirty years later". (17)
When the night staff arrived for work just before midnight on 4th June, 1944 they were informed that tomorrow was D-Day: "They told us that D-Day was today and they wanted every possible message decoded as fast as possible. But then it was postponed because the weather was so bad and that meant we girls knew it was going to take place, so we had to stay there until D-Day. We slept where we could and worked when we could and of course then they set off on June 6, and that was D-Day." (18)
Winston Churchill and his commanders wanted to know if the deception plans for the D-Day landings had been successful. Developed by two agents, Tomás Harris and Juan Pujol: The key aims of the deception were: "(a) To induce the German Command to believe that the main assault and follow up will be in or east of the Pas de Calais area, thereby encouraging the enemy to maintain or increase the strength of his air and ground forces and his fortifications there at the expense of other areas, particularly of the Caen area in Normandy. (b) To keep the enemy in doubt as to the date and time of the actual assault. (c) During and after the main assault, to contain the largest possible German land and air forces in or east of the Pas de Calais for at least fourteen days." (19)
Harris devised a plan of action for Pujol (code name GARBO). He was to inform the Germans that the opening phase of the invasion was under way as the airborne landings started, and four hours before the seaborne landings began. "This, the XX-Committee reasoned, would be too later for the Germans to do anything to do anything to frustrate the attack, but would confirm that GARBO remained alert, active, and well-placed to obtain critically important intelligence." (20)
Christopher Andrew has explained how the strategy worked: "During the first six months of 1944, working with Tomás Harris, he (GARBO) sent more than 500 messages to the Abwehr station in Madrid, which as German intercepts revealed, passed them to Berlin, many marked 'Urgent'... The final act in the pre-D-Day deception was entrusted, appropriately, to its greatest practitioners, GARBO and Tomás Harris. After several weeks of pressure, Harris finally gained permission for GARBO to be allowed to radio a warning that Allied forces were heading towards the Normandy beaches just too late for the Germans to benefit from it." (21)
Tommy Flowers had a meeting with General Dwight D. Eisenhower on 5th June. He was able to tell Eisenhower that Adolf Hitler was not sending any extra troops to Normandy and still believed that the Allied troops would land east of the Pas de Calais. Flowers was also able to report that Colossus Mark II had decoded message from Field Marshal Erwin Rommel that one of the drop sites for an US parachute division was the base for a German tank division. As a result of this information the drop site was changed.
Jean Thompson later explained her role in the operation in the book, Station X: The Codebreakers of Bletchley Park (1998): "Most of the time I was doing wheel setting, getting the starting positions of the wheels. There would be two Wrens on the machine and a duty officer, one of the cryptanalysts - the brains people, and the message came in on a teleprinted tape. If the pattern of the wheels was already known you put that up at the back of the machine on a pinboard. The pins were bronze, brass or copper with two feet and there were double holes the whole way down the board for cross or dot impulses to put up the wheel pattern. Then you put the tape on round the wheels with a join in it so it formed a complete circle. You put it behind the gate of the photo-electric cell which you shut on it and, according to the length of the tape, you used so many wheels and there was one moveable one so that could get it taut. At the front there were switches and plugs. After you'd set the thing you could do a letter count with the switches. You would make the runs for the different wheels to get the scores out which would print out on the electromatic typewriter. We were looking for a score above the random and one that was sufficiently good, you'd hope was the correct setting. When it got tricky, the duty officer would suggest different runs to do." (22)
Peter Hilton has suggested that Max Newman was an outstanding leader of men: "He realised that he could get the best out of us by trusting to our own good intentions and our strong motivation and he made the thing always as informal as possible. For example, he gave us one week in four off. We would be just encouraged to do research on our cryptanalytical methods. Of course, the research work should always be related to the job and we always wrote down what we were thinking in a huge book so that it could be preserved and some of those ideas were adopted and became part of the procedure. So I think Newman was the model administrator." (23)
Jack Good claims that "Newman ran this large section with the natural authority of a father figure, but in a democratic spirit. He took pleasure in the achievements of his staff, and originality flourished." Newman would also invite those who were not cryptanalysts to contribute their ideas. (24) George Vergine pointed out: "Max Newman was a marvellous fellow I always sort of felt grateful to have known him really. We used to have tea parties. These were just discussions on problems or developments, techniques, to a great extent mathematical. We used to meet in the small conference room. Somebody would write a topic up on the blackboard and all of the analysts, including Newman, would come with their tea in hand and chew it around and see whether or not it would be useful as far as cracking more communications. They were very productive and after it was over somebody would summarise it in the research log." (25)
University of Manchester
After the war Max Newman was professor of mathematics at the University of Manchester. In 1948 Alan Turing joined the department. When Turing was arrested and charged with gross indecency under Section 11 of the Criminal Law Amendment Act 1885, in 1952, Newman and Hugh Alexander agreed to appear as character witnesses. (26) However, Turing was found guilty and committed suicide on 7th June, 1954.
Jack Good recalls that "Newman was a very gifted pianist and a good chess player. His technique for solving chess problems was to consider the function of a seemingly irrelevant piece.... At first contact perhaps austere, he was in fact a splendid companion." (27) After the death of his first wife, Lyn Lloyd Newman, in 1973, he married Dr Margaret Penrose.
Max Newman died in Cambridge on 22nd February 1984.
Primary Sources
(1) Simon Singh, The Code Book: The Secret History of Codes & Code-Breaking (2000)
During the Second World War, British codebreakers had the upper hand over German codemakers, mainly because the men and women at Bletchley Park, following the lead of the Poles, developed some of the earliest codebreaking technology. In addition to Turing's bombes, which were used to crack the Enigma cipher, the British also invented another codebreaking device, Colossus, to combat an even stronger form of encryption, namely the German Lorenz cipher. Of the two types of codebreaking machine, it was Colossus that would determine the development of cryptography during the latter half of the twentieth century.
The Lorenz cipher was used to encrypt communications between Hitler and his generals. The encryption was performed by the Lorenz SZ40 machine, which operated in a similar way to the Enigma machine, but the Lorenz was far more complicated, and it provided the Bletchley codebreakers with an even greater challenge. However, two of Bletchley's codebreakers, John Tiltman and Bill Tutte, discovered a weakness in the way that the Lorenz cipher was used, a flaw that Bletchley could exploit and thereby read Hitler's messages.
Breaking the Lorenz cipher required a mixture of searching, matching, statistical analysis and careful judgement, all of which was beyond the technical abilities of the bombes. The bombes were able to carry out a specific task at high speed, but they were not flexible enough to deal with the subtleties of Lorenz. Lorenz-encrypted messages had to be broken by hand, which took weeks of painstaking effort, by which time the messages were largely out of date. Eventually, Max Newman, a Bletchley mathematician, came up with a way to mechanise the cryptanalysis of the Lorenz cipher. Drawing heavily on Alan Turing's concept of the universal machine, Newman designed a machine that was capable of adapting itself to different problems, what we today would call a programmable computer.
Implementing Newman's design was deemed technically impossible, so Bletchley's senior officials shelved the project....Colossus, as with everything else at Bletchley Park, was destroyed after the war, and those who worked on it were forbidden to talk about it. When Tommy Flowers was ordered to dispose of the Colossus blueprints, he obediently took them down to the boiler room and burnt them. The plans for the world's first computer were lost for ever. This secrecy meant that other scientists gained the credit for the invention of the computer. In 1945, J. Presper Eckert and John W Mauchly of the University of Pennsylvania completed ENIAC (Electronic Numerical Integrator And Calculator), consisting of 18,000 electronic valves, capable of performing 5,000 calculations per second. For decades, ENIAC, not Colossus, was considered the mother of all computers.
Having contributed to the birth of the modern computer, cryptanalysts continued after the war to develop and employ computer technology in order to break all sorts of ciphers. They could now exploit the speed and flexibility of programmable computers to search through all possible keys until the correct one was found. In due course, the cryptographers began to fight back, exploiting the power of computers to create increasingly complex ciphers. In short, the computer played a crucial role in the postwar battle between codemakers and codebreakers.
Using a computer to encipher a message is, to a large extent, very similar to traditional forms of encryption. Indeed, there are only three significant differences between computer encryption and the sort of mechanical encryption that was the basis for ciphers like Enigma. The first difference is that a mechanical cipher machine is limited by what can be practically built, whereas a computer can mimic a hypothetical cipher machine of immense complexity. For example, a computer could be programmed to mimic the action of a hundred scramblers, some spinning clockwise, some anticlockwise, some vanishing after every tenth letter, others rotating faster and faster as encryption progresses. Such a mechanical machine would be practically impossible to build, but its `virtual' computerised equivalent would deliver a highly secure cipher.The second difference is simply a matter of speed. Electronics can operate far more quickly than mechanical scramblers: a computer programmed to mimic the Enigma cipher could encipher a lengthy message in an instant. Alternatively, a computer programmed to perform a vastly more complex form of encryption could still accomplish the task within a reasonable time.
The third, and perhaps most significant, difference is that a computer scrambles numbers rather than letters of the alphabet. Computers deal only in binary numbers - sequences of ones and zeros known as binary digits, or bits for short. Before encryption, any message must therefore be converted into binary digits.
(2) Michael Smith, Station X: The Codebreakers of Bletchley Park (1998)
Max Newman, one of the mathematicians working in the Testery, became convinced that, using the principles advocated by Turing in his pre-war treatise on a computing machine, it would be possible to build a machine that, once the patterns of the wheels had been worked out in the Testery, would find the settings of the first row of wheels, thereby making the codebreakers' task immeasurably easier.
Newman, an academic from Cambridge University, took his ideas to Travis and received the necessary backing and promise of funding to set up his own section, which became known as the Newmanry. He then went to Wynn-Williams at the Telecommunications Research Establishment in Malvern and asked him to design the machine.
It was known as 'Robinson', after Heath Robinson, the cartoonist designer of fantastic machines, and the first version was delivered to Bletchley Park in May 1943. It worked on the principle that although the encyphering letters were supposed to be random, they were not. No machine can generate a truly random sequence of letters. Robinson compared a piece of teleprinter tape carrying the encyphered text with a piece of tape on which the wheel patterns had been punched to look for statistical evidence that would indicate what the wheel-settings were.Robinson was designed to keep the two paper tapes in synchronisation at a thousand characters a second but at that speed the sprocket wheels kept ripping the tapes. Turing who, while working on the bombe, had been impressed by the abilities of a bright young telephone engineer at Dollis Hill called Tommy Flowers, suggested to Newman that he might be just the man to get Robinson to work.
'I came into the project when the Robinson machine didn't work properly, because it was made almost entirely of telephone parts, telephone switching parts, which was my area,' Flowers said. 'I was brought in to make it work, but I very soon came to the conclusion that it would never work. It was dependent on paper tape being driven at very high speed by means of spiked wheels and the paper wouldn't stand up to it.'
Tester recalled long conversations with Flowers, Turing, Tutte and Newman over what should be done. Flowers, who had been developing telephone exchanges containing valves instead of the old-fashioned relays used in Robinson, suggested that he could make an electronic machine built with valves that would do the same job much faster without the need for the synchronisation of the two tapes. The data on the wheel patterns would be generated electronically using ring circuits while the tape reading the cypher text would be read photo-electrically and could be run on smooth wheels rather than sprockets so it wouldn't rip....
Colossus was the first practical application of a large-scale program controlled computer and as such the forerunner of the post-war digital computer. Although it had a specialised function, it showed that Turing's theory could be turned into practice. The sequence of operations was determined mainly by setting of external switches and plugboards, which were controlled by Wrens on the orders of the Newmanry codebreakers. Just like the Robinson, it was looking for sequences that were not random. "The work on Tunny divided roughly between what you might call the machine work and the hand work," Halton recalled. "Machine work was of course putting messages on to Colossus which was a process whereby we would determine the starting positions of the first set of five wheels which were involved in making up the key. Then after that process had taken place, that is to say a process based on statistics, mathematics, the message shorn of part of its key would come to the codebreakers in the Testery who would then have the job of using their knowledge of expected pieces of text in order to set the remaining wheels."
(3) George Vergine, quoted by Michael Smith, the author of Station X: The Codebreakers of Bletchley Park (1998)
When I arrived, the first Colossus was in a new area that they had acquired for expansion and I think two of the Robinsons, the previous diagnostic machines, were operating. There must have been probably fifteen mathematically minded analysts. There were probably ten Wrens on a shift, processing the tapes. There was a lot of background of mathematics and techniques to catch up on.
Colossus was the epitome of an adult toy. For the mathematicians it was marvellous. It would tabulate five thousand frames of teleprinter tape a second so if you did a run for ten minutes you were probably getting close to three million tallies. It was fascinating really. You didn't see plain text, the Testery was the one that recovered the plain text. You were dealing entirely in a statistical world.
You would toss out the random scores and look for anything that looked like it was causal. The operator had to make a decision when he got the final scores, on the spot. You made that decision right there, in your head, sitting on a stool in front of Colossus. You depended entirely on the probability of being right as far as the random scores were concerned. If you got a causal score you would try to confirm it one way or the other on some of the other wheels, or by another run...
Max Newman was a marvellous fellow I always sort of felt grateful to have known him really. We used to have tea parties. These were just discussions on problems or developments, techniques, to a great extent mathematical. We used to meet in the small conference room. Somebody would write a topic up on the blackboard and all of the analysts, including Newman, would come with their tea in hand and chew it around and see whether or not it would be useful as far as cracking more communications. They were very productive and after it was over somebody would summarise it in the research log.
(4) Jean Thompson, quoted by Michael Smith, the author of Station X: The Codebreakers of Bletchley Park (1998)
Most of the time I was doing wheel setting, getting the starting positions of the wheels. There would be two Wrens on the machine and a duty officer, one of the cryptanalysts - the brains people, and the message came in on a teleprinted tape.
If the pattern of the wheels was already known you put that up at the back of the machine on a pinboard. The pins were bronze, brass or copper with two feet and there were double holes the whole way down the board for cross or dot impulses to put up the wheel pattern. Then you put the tape on round the wheels with a join in it so it formed a complete circle. You put it behind the gate of the photo-electric cell which you shut on it and, according to the length of the tape, you used so many wheels and there was one moveable one so that could get it taut.
At the front there were switches and plugs. After you'd set the thing you could do a letter count with the switches. You would make the runs for the different wheels to get the scores out which would print out on the electromatic typewriter. We were looking for a score above the random and one that was sufficiently good, you'd hope was the correct setting. When it got tricky, the duty officer would suggest different runs to do.
(5) Peter Hilton, quoted by Michael Smith, the author of Station X: The Codebreakers of Bletchley Park (1998)
He realised that he could get the best out of us by trusting to our own good intentions and our strong motivation and he made the thing always as informal as possible. For example, he gave us one week in four off. We would be just encouraged to do research on our cryptanalytical methods. Of course, the research work should always be related to the job and we always wrote down what we were thinking in a huge book so that it could be preserved and some of those ideas were adopted and became part of the procedure. So I think Newman was the model administrator.
